Security and trust, built into every layer
Comprehensive protection with user authentication, data encryption, AI guardrails, and platform resiliency.
Authenticate users with precision and confidence
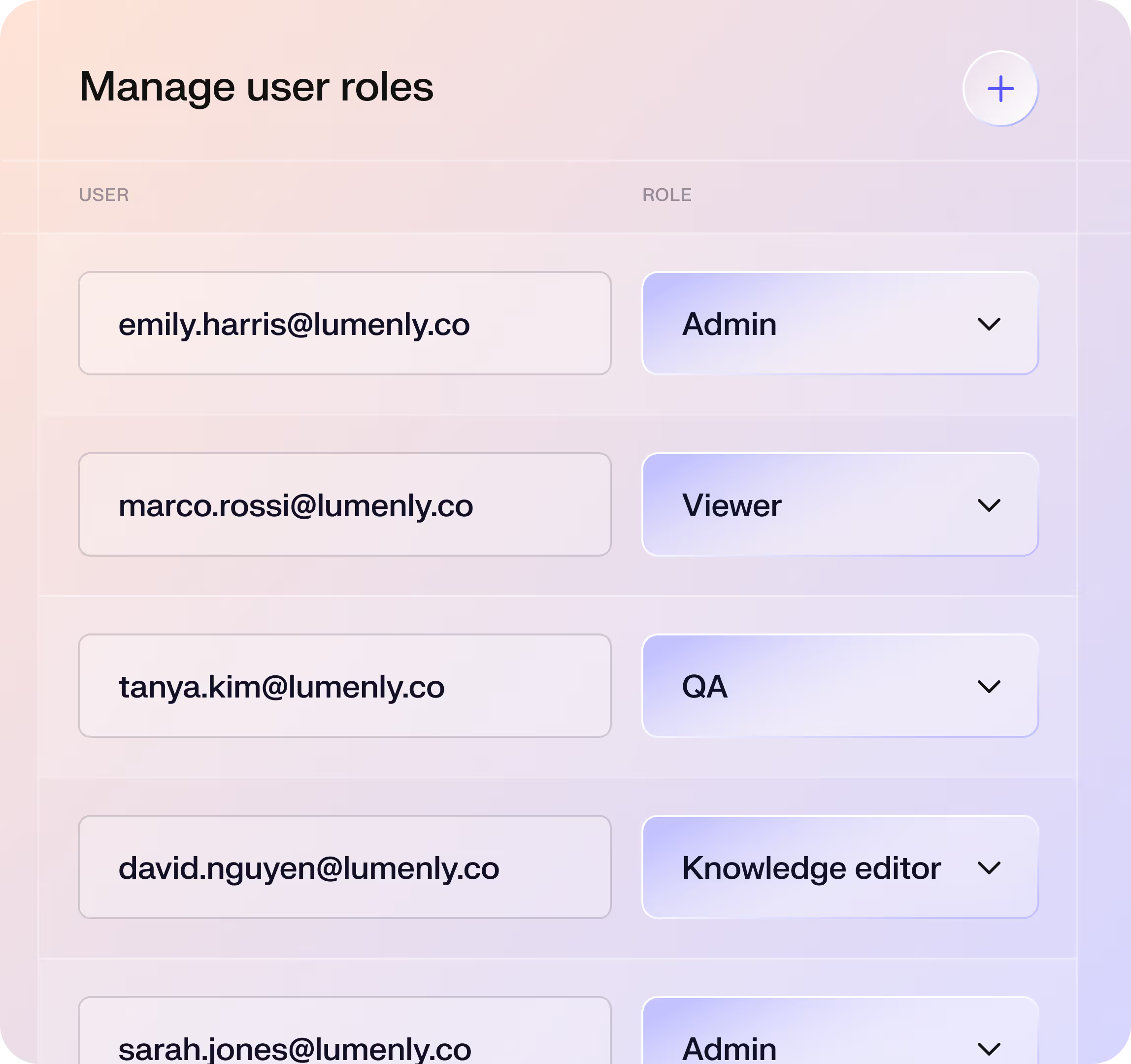
Role-Based Access Control (RBAC)
Platform access is defined and enforced by role, ensuring every user automatically gets the right permissions for their job.
Single Sign-On (SSO)
Decagon integrates with identity providers like Okta and Microsoft Entra, enabling secure access across systems without additional passwords.
Just-in-time API tokens
Short-lived JWT tokens give AI agents real-time access to customer systems, scoped for minimal privilege and discarded after each session.
Voice authentication
Flexible authentication methods to verify end-users over voice channels, providing strong protection for sensitive workflows.
Protect your data, from storage to transmission
Encryption at rest and in transit
Data is encrypted automatically at every stage: AES-256 for storage and backups, and TLS 1.2+ for all network transmission.
Secure key management
Encryption keys are centrally managed with strict access controls, expiration policies, and rotation schedules that maintain continuous protection.
Zero-day retention with LLMs
Decagon enforces zero-day retention with all AI providers like OpenAI and Anthropic, ensuring no conversation data is stored or used for training.
PII redaction
Sensitive data is automatically detected and redacted using Google’s DLP service, sanitizing logs and transcripts just after a conversation ends.
.avif)
Ensure safe, transparent, and accountable AI performance
Bad actor detection
A specialized detection system identifies adversarial prompts, manipulation attempts, or policy violations, deflecting unsafe inputs or escalating to a human.
Supervisor model
A built-in supervisor detects hallucinations before responses are sent, automatically revising responses that stray from factual grounding.
Watchtower
An always-on QA system that reviews every conversation against your custom criteria, flagging compliance risks or outlier behavior for rapid triage.
Audit logs
Comprehensive, tamper-protected logs capture key events, from logins to unusual activity, accessible only to senior engineering leadership.
.avif)





Provide instant, reliable support that never sleeps
Multi-region infrastructure
Model redundancy
Platform uptime SLAs
Autoscaling and auto-failover
Ongoing health checks
Bring agility to your enterprise
Explore how the world’s leading enterprises use Decagon to achieve exceptional results.
"Rippling has a very broad surface area with distinct products that require unique treatments — we brought this problem statement to Decagon and they delivered. We are able to tailor the experience and responses to customers to not only deliver strong deflection results, but also enhance the customer experience along the way. We are very happy with our results and are looking forward to partnering further with Decagon."
Though we already had a robust Voice of the Customer program and an understanding of customer inquiries we thought we could deflect, we saw 10x higher deflection at launch than we anticipated.




